One of the most worrying leaks arising from the recent WikiLeaks publication is the possibility that government organizations can compromise WhatsApp, Telegram, and other end-to-end encrypted chat applications. While this has yet to be proven, many end-users are concerned about WhatsApp and Telegram end-to-end encryption to guarantee user privacy. This encryption is designed to ensure that only the people communicating can read the messages and nobody else in between.

But, this same mechanism has also been the origin of a new vulnerability we have discovered in both messaging service online platforms WhatsApp Web and Telegram Web. The online version of these platforms mirror all messages sent and received by the user and are fully synced with the users’ device.
This vulnerability, if exploited, would have allowed attackers to completely take over users’ accounts on any browser, and access victims’ personal and group conversations, photos, videos and other shared files, contact lists, and more. This means attackers could possibly download your photos and or post them online, send messages on your behalf, demand ransom, and even take over your friends’ accounts.

So, next time when someone sends you a photo of a cute cat or a hot chick on WhatsApp or Telegram, then be careful before you click on the image to view, it might hack your account within seconds. A computer security firm on Wednesday revealed a flaw that could let hackers break into WhatsApp or Telegram messaging accounts using the very encryption intended to protect messages.
Technical Details – WhatsApp
WhatsApp upload file mechanism supports several document types such as Office Documents, PDF, Audio files, Videos, and images. Each of the supported types can be uploaded and sent to WhatsApp clients as an attachment.
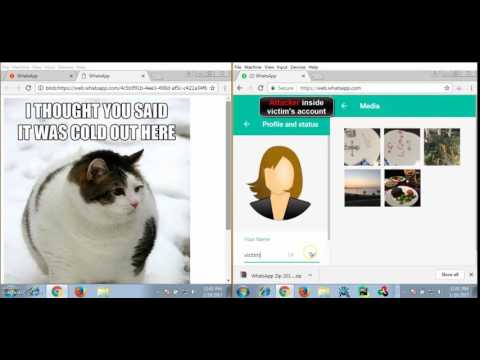
However, Check Point research team has managed to bypass the mechanism’s restrictions by uploading a malicious HTML document with a legitimate preview of an image in order to fool a victim to click on the document in order to take over his account. Once the victim clicks on the document, the WhatsApp web client uses the FileReader HTML 5 API call to generate a unique BLOB URL with the file content sent by the attacker then navigates the user to this URL.
Technical Details – Telegram
Telegram supports multiple document types to be sent to the Telegram Web application, but the only image and video document types are stored in the Filesystem section within the browser.

Check Point researchers have managed to bypass Telegram’s upload policy and upload a malicious HTML document with a mime type of a video file “video/mp4”. Then, they were able to send it to the victim side in an encrypted channel through telegram servers. Once the victim opens the video in a new browser tab, it will start playing and the users’ session data will be sent to the attacker.
Interestingly, it’s the end-to-end encryption feature of these apps that would have helped hackers take advantage of the flaw. Because the contents of chats are end-to-end encrypted, it means that neither WhatsApp nor Telegram could see the malware hidden in a shared malicious image. That means both companies would be blind to the content, allowing malicious code to be passed back and forth between users.
Henceforward, content will be validated before the encryption, Check Point explains, which would block malicious files. The Check Point team also outlines a couple of methods to make sure that you aren’t victims of such hacks.

Check Point Security Tips:
While WhatsApp & Telegram have patched this vulnerability, as a general practice we recommend the following preventive measures:
1. Periodically clean logged-in computers from your WhatsApp & Telegram. This will allow you to control the devices that are hosting your account and shut down unwanted activity.
2. Avoid opening suspicious files and links from unknown users.
After fixing this flaw, content on the web versions of both WhatsApp and Telegram will now be validated before the end-to-end encryption comes into play, allowing malicious files to be blocked.
